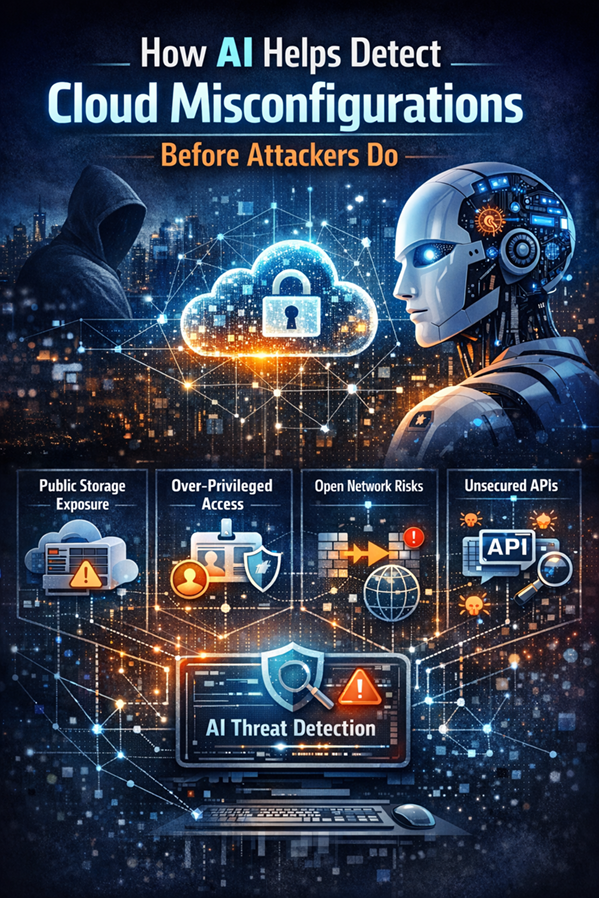
Cloud environments provide speed and flexibility, but they also introduce new security risks. One of the most common causes of cloud breaches is misconfiguration. Public storage accounts, overly permissive identities, and open network rules can expose sensitive resources to attackers.
In large cloud environments, manually detecting these issues is difficult. Organizations deploy hundreds or thousands of resources across services like Azure App Service, Azure Storage, Azure SQL, and Azure Kubernetes Service. Security teams need automated ways to continuously monitor configurations and detect risks.
This is where Artificial Intelligence (AI) plays a key role.
The Misconfiguration Problem in Cloud Security
Cloud misconfigurations typically occur when resources are deployed with insecure settings. Common examples include:
- Publicly accessible Azure Storage accounts
- Excessive permissions in Azure RBAC
- Misconfigured Network Security Groups (NSGs)
- Disabled logging or monitoring
- Exposed APIs or services
Attackers continuously scan cloud environments looking for these weaknesses. Once discovered, they can quickly gain access to sensitive data or infrastructure.
Traditional security tools rely on static rules and manual audits, which are often too slow for dynamic cloud environments.
AI-Driven Detection in Microsoft Cloud Security
Microsoft integrates AI and machine learning into several security platforms to help detect cloud risks earlier.
Microsoft Defender for Cloud
Microsoft Defender for Cloud continuously analyzes Azure resources and configurations. It uses AI and threat intelligence to identify misconfigurations such as:
- publicly exposed storage
- unprotected virtual machines
- excessive identity permissions
- insecure network configurations
The platform also prioritizes risks using Secure Score and highlights exploitable attack paths across cloud resources.
Attack Path Analysis
A powerful capability in Defender for Cloud is attack path analysis. Instead of showing isolated issues, the system identifies combinations of misconfigurations that attackers could exploit.
For example:
- an over-privileged service account
- access to sensitive storage
- external network exposure
AI helps correlate these signals and reveal potential attack paths before they are exploited.
AI and Identity Risk Detection
Identity is often the entry point for cloud attacks. Microsoft Entra ID Identity Protection uses machine learning to detect suspicious identity behaviors such as:
- abnormal sign-in patterns
- credential misuse
- risky authentication attempts
These signals can help identify compromised accounts that might attempt to exploit misconfigured resources.
Why AI Matters for Security Teams
AI allows security platforms to process massive amounts of cloud telemetry and highlight the most critical risks. Instead of reviewing thousands of alerts, security teams can focus on high-impact issues.
AI helps by:
- identifying abnormal configuration changes
- correlating security signals across services
- prioritizing exploitable risks
- reducing false positives
This improves the ability of security teams to detect and remediate misconfigurations quickly.
Final Thoughts
Cloud misconfigurations remain one of the most common causes of security incidents. As cloud environments grow more complex, manual monitoring becomes impractical.
By integrating AI into platforms such as Microsoft Defender for Cloud and Entra ID, organizations can detect risky configurations earlier and reduce their attack surface.
AI does not replace security professionals, but it enables them to identify threats faster and focus on the most critical risks before attackers do.